located at System Setup > LDAP Web Service Settings. Each LDAP-WS entry contains all the necessary settings to make a successful call to a LDAP-WS tenant.
LDAP-WSuses SSL certificate mutual authentication binding between LDAP-WS and the client (in this case, Safewhere*Identify). This type of binding requires that:
- A LDAP-WS tenant must have its own certificate (referred to as the server certificate in the remainder of the section).
- A client which needs to communicate with LDAP-WS must also have its own certificate (referred to as the client certificate in the remainder of the section).
- The machine, which the LDAP-WS is running on must trust the client certificate. This means that the public key of the client certificate must be imported to the LocalMachine/TrustedPeople store on the server machine.
The machine which the client is running on must trust the server certificate. This means that the public key of the server certificate must be imported to LocalMachine/TrustedPeoplestore on the server machine.
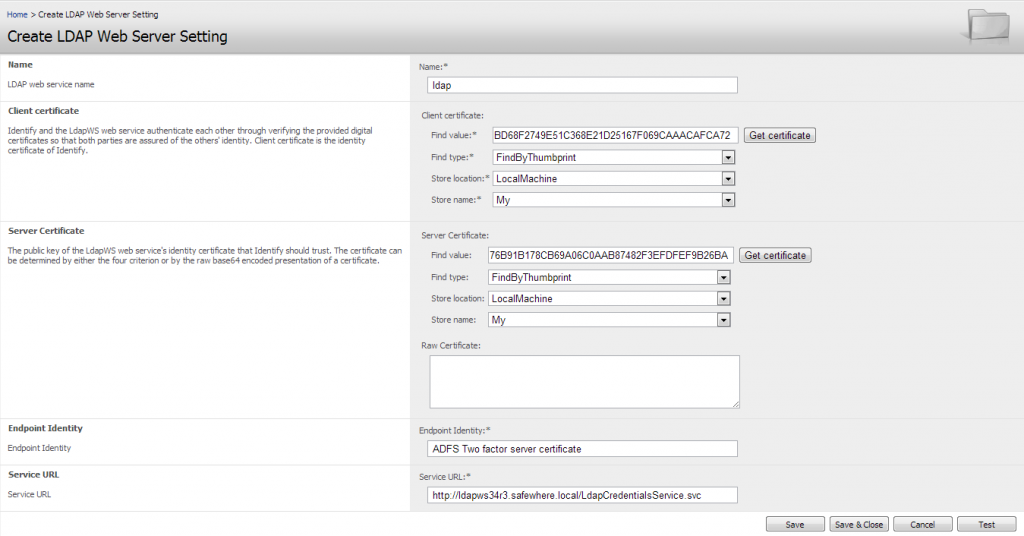
UI fields are explained below:
- Name: A unique name for a LDAP Web Service Settings. This name only need to be meaningful in Identify’s context.
- Client Certificate: Setting for client certificate including StoreLocation, StoreName, FindType andFindValue. All fields are required.
- Server Certificate: Setting for server certificate including StoreLocation, StoreName, FindType, FindValue and Raw certificate. You can fill in either Raw certificate directly or the four fields.
- Endpoint identity: The server certificate’s subject, it’s autogenerated after inputing the server certificate.For instance, “LDAPWSDEMO5 SERVERCERTIFICATE”.
- Server Url: Specifies the fully qualified domain name of the LDAP Web Service Server (or the URL we call API). For instance, “http://ldapwsdemo5.safewhere.local/LdapCredentialsService.svc”.
There is also a button named Test, which can be used to validate the configuration (that is, to ensure that Identify is able contact LDAP-WS). Please remember to save before pressing “Test”.