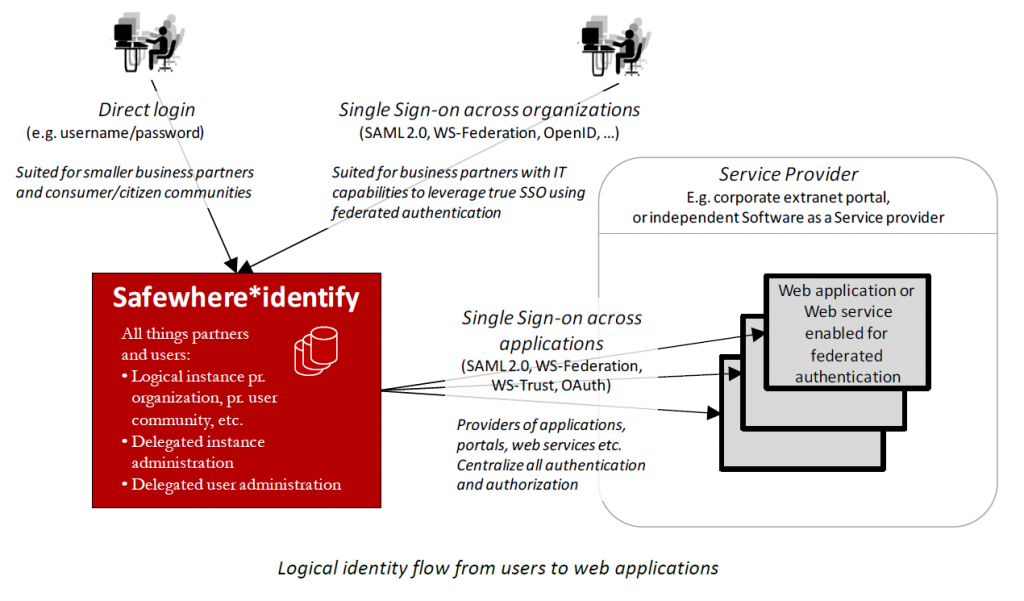
Safewhere*Identify allows an organization to handle user identification and administration centrally and externally to all web applications and web services. Safewhere*Identify allows you to support any kind of authentication due to its modular and open nature and it supports many authentication methods “out of the box”. Apart from built-in methods for authentication such as username and password, it also supports all the popular authentication methods, including
- Social logins from Facebook, Google, Twitter, Live ID, OpenID, LinkedIn.
- Two-factor authentication using one time password and Device Code authentication.
- Federation protocols including SAML 2.0, WS-Federation, OpenID Connect, and OAuth 2.0.
- Generic Provider that allows you to create your own authentication provider with ease.
Selected benefits and advantages include
- Self-service user administration: Safewhere*Identify provides a separate instance per organization for authentication and maintenance of user attributes. Each instance belongs to, and is administered by, one organization.
- Externalization of authentication: All the authentications to your applications and services will be transferred to Safewhere*Identify – “Identity broker”, which in turn integrates with the desired authentication mechanisms and user databases.
- Application integration: As more and more of your applications exploit the new identity solution, your users will experience seamless Single sign-on (SSO) across applications. Safewhere*Identify provides identity conversion/mapping to successfully transfer identities between applications.
- Provided both “as a service” and as traditional on premise software: Due to the unique and standards compliant architecture and communication patterns, Safewhere*Identify may equally well be leveraged as an external service (Software as a Service) or as software installed in your own infrastructure. Whichever is chosen has no effect on feature set or security.
-
Self-registration of organizations and users: Workflows support the signing of new organizations – e.g. new business partners – as well as new users of each organization. The first requires review and approval of you whereas the latter leverages the distributed nature of user administration and leaves it up to the user’s home organization.